Mapped to Policy and Standard Control Requirements
(NIST 800-53r5 | FIPS 199 Categorization Aligned)
NOTICE
Following the ComplianceForge Hierarchical Cybersecurity Governance Framework (HCGF), these Procedures fully align with and support WSU UPPM 87.23 Control Exception Policy and Standard control objectives. WSU Business Units integrating these Procedures into their business processes with Standardized Operating Procedures (SOPs) would be demonstrating compliance with UPPM 87.23 Control Exception Policy.
Responsibilities and Governance
NIST Security Controls: RA-3
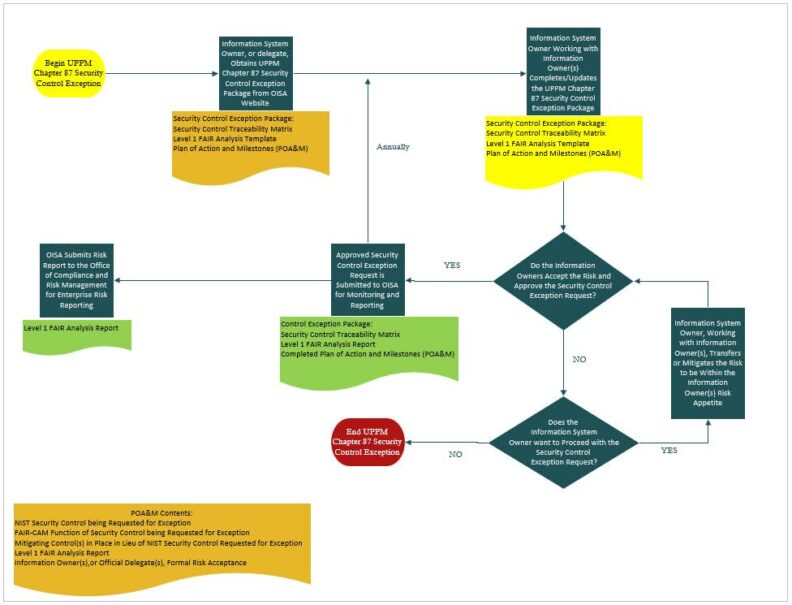
- The Office of Information Security and Assurance (OISA) provide executive sponsorship for the Security Control Exception Process (Appendix A) and reviews the Process on an annual basis.
- OISA maintains the Security Control Exception Standard and provides guidance for implementing the policy.
- OISA monitors and reports on approved Security Control Exception Requests in accordance with UPPM 87.25.
- Information System Owners, or their delegates, are responsible and accountable for developing and maintaining SOPs required to implement this procedure for their information systems.
Security Control Exception Request
NIST Security Controls: RA-3
- Security Control Exception Requests are performed when an Information System Owner, or delegate, is unable to implement the security control objective of a UPPM Chapter 87 policy or standard statement for an information system under their care.
- Information System Owners, or their delegates, obtain the Security Control Exception Request package from OISA’s website when conditions exist that prohibit the ability for the WSU Area to implement a UPPM Chapter 87 policy statement or standard statement.
- The Security Control Exception Package includes the impacted policy and/or standard statement(s), the scope of the exception, affected information system(s), a security controls traceability matrix, a risk analysis template, and a POA&M template.
- Information System Owners, or their delegates, coordinate and work with the affected and appropriate Information Owners, or their delegates, to complete the Security Control Exception package and obtain the Information Owner(s) documented Risk Treatment Plan in a Plan of Action and Milestones (POA&M) in
accordance with UPPM 87.25. - The risk associated with increased variance in security controls, including expected frequency and magnitude of potential loss, is assessed and communicated to appropriate risk owners for treatment.
- A risk assessment is conducted to support the Security Control Exception decision, including identifying threats and vulnerabilities, determining the likelihood and magnitude of harm, and determining probable financial loss to WSU.
- Risk assessment results and risk management decisions are integrated from organization and mission or business process perspectives with system-level risk assessments.
- Risk assessments are performed collaboratively by Information Owners and Information System Owners using the resources in the Security Control Exception Package to assess probable loss frequency and probable loss magnitude resulting from the control variance to inform risk treatment decisions.
- Completed and approved Security Control Exception Requests must be submitted to OISA, for monitoring and reporting, to be valid Security Control Exceptions.
- Risk assessment results are documented in security and privacy plans, a risk assessment report, and/or other area-defined documentation supporting the Security Control Exception decision.
- Risk assessment results are disseminated to area-defined personnel or roles involved in the Security Control Exception decision and WSU’s Enterprise Risk Management program.
- Security Control Exception Requests are reviewed and updated at least annually and/or when significant system or environmental changes occur.
- Security Control Exceptions are closed when remediation is completed, when the exception is no longer required, or when the approved exception period expires without renewal by the Information Owner.
- Security Control Exception Closure Evidence is retained in area-defined records.
Training and Awareness
Training requirements align with UPPM 87.21.
- Information System Owners, or their delegates, ensure that users receive appropriate information security and privacy training commensurate with their roles, responsibilities, and authorized access to information systems under the Information System Owner’s authority.
Appendix A – Revision History:
| Version No. | Date | Description | Author |
|---|---|---|---|
| 1.0 | 01/01/2026 | Initial Release Procedure publication for 87.23 Policy | OISA GRC |
| 1.1 | 02/12/2026 | Added HCGF Link | OISA GRC |